KNX SECURITY
Content
- Introduction
- Making KNX Security
- What is KNX Data Security
- What is KNX IP Secuity
- KNX IP Routing & Tunneling
- Mixed Security installation
Introduction
Protecting installations from inside and outside
Communication and data processing are hardly conceivable today without considering security aspects. Indeed, insecure communication systems are fast becoming unacceptable. The way has already been shown by the Internet, with the well-known ‘http’ protocol from 1991 having been largely replaced by the encrypted ‘https’ variant. Incidentally, one year earlier than http, the KNX system was launched in 1990 under the name EIB.
Even in buildings, the need for secure communication can no longer be overlooked. At present, despite reports of tampering, there may be little concrete evidence of actual damage by hackers, but their efforts are only likely to increase, so it is necessary to counter potential dangers for technical infrastructure.
The web browser error message below, about the lack of security, should also serve as a warning for building technology.

More about KNX Security
Videos about KNX Security
These devices support KNX Security
Making KNX secure
As an association of manufacturers, the KNX Association embraced the subject of security at an early stage under the title ‘KNX Security’. Specification and implementation took several years; a major reason being the complexity of the KNX protocol, for which group addressing, which is essential to the entire KNX system, is quite a challenge for secure encryption.
By the beginning of 2019, both the system and test specifications were considered stable and were approved by the KNX Association Technical Board. In addition, the KNX Association invested a great deal of effort in implementing the security theme in the ETS – the central installation software for KNX. The test tools for the development of KNX Security devices were also extended accordingly, and certified KNX Security products are now available.
So, now that KNX Security is a reality, let’s look in more detail with its two variants, namely KNX Data Security and KNX IP Security.
What is KNX Data Security
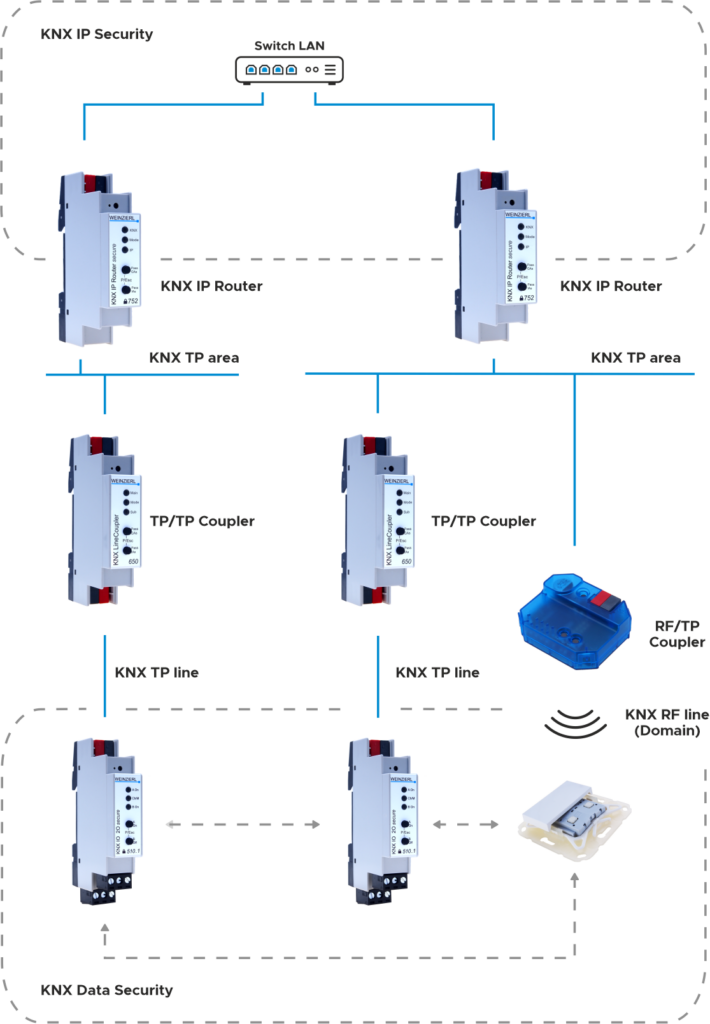
KNX Data Security aims to secure communication at the telegram level. It can be used independently of the KNX medium both for commissioning and for runtime communication. KNX Data Security protects the communication within the KNX installation.


What is KNX IP Security
KNX IP Security follows an alternative approach, but is based on the same encryption methods as KNX Data Security. KNX IP Security is a pragmatic approach based on the assumption that there is a point of attack at the IP level. Whereas KNX Twisted Pair is assumed to be relatively secure as a purely local medium located in the wall, IP communication is often connected to the Internet and can therefore be attacked remotely.
KNX IP Security protects KNX IP Communication whilst communication on KNX TP remains unencrypted. KNX IP Security protects the KNX installation from intruders.
KNX IP Routing & Tunneling
Which is used for IP backbones, but also represents the KNX IP medium. On the other hand, the tunnelling protocol is used to enable a client (e.g. ETS) to access a TP line via IP. While KNX IP routers usually implement both protocols, KNX IP interfaces only support the tunnelling function.
Mixed security installations
Since it is not expected that all required devices will be available as a secure variant at short notice, it is important that secure and insecure communication can be mixed in one installation. The secure property is defined at group level. If two group objects that both support security are connected, the ETS proposes a secure link. However, if just one object is in a group without security, the entire group must communicate insecurely.